Bit of a different post from me today, I wanted to talk about 50 IT acronyms and what they mean as I’ve found most people don’t know these. Or you might know them intuitively, but not have an understanding of them.
Before we start, you can check this out on Medium!
Introduction
Not much of an introduction is needed really. I’ll be listing 50 common acronyms within the world of digital technology. Most you’ll have heard of before, but you might not have an understanding of them. Others, you won’t have heard of.
50 IT Acronyms And What They Mean
I’ll be going through them in alphabetical order. Lets jump straight in!
3G/4G/5G
Have you ever wondered what 3G, 4G or 5G is? You’re not the only one! These are all distinct generations of mobile com standards. As you’d expect, 5G is newer than 4G and 4G is newer than 3G.
3G was initially released in the early 2000’s. 4G rolled out in the late 2000’s, early 2010’s and offered a much safer service over 3G. Finally, 5G is the latest version of the standard and is still being adopted in a bunch of locations.
AES
Standing for Advanced Encryption Standard, this is a symmetric encryption algorithm used for all modern encryption. Initially developed by the US National Institute of Standards and Technology and replaced the defunct DES standard.
With fixed block sizes of 128 bits and key sizes ranging from 128, 192 and 256 bits, AES also have a number of rounds and this depends on the key size. 10 rounds for 128 bit, 12 rounds for 192 bit and finally 14 rounds for 256 bit keys.
API
API stands for Application Programming Interface and at it’s most basic form, allows two computer systems to communicate together using a standard set of rules and protocols.
Whenever you hear API, think of an interpreter or translator. Instead of you struggling to learn a new language when meeting someone, you can instead use a middle person to translate what you want.
AR
AR stands for Augmented Reality and is distinctly different from VR since it doesn’t create a completely digital world. Instead, AR works to augment the real world around you.
This technology is often used to enhance real world interactions. A great example of this is the Pokémon cards that pop up a little virtual character on your phone. And if you know what I’m talking about, sorry for bringing back those memories!
BIOS
A BIOS is the Basic Input/Output System and is used as the fundamental software found in most technology. It’s main function is to facilitate the most basic functions, such as powering up the system, storing basic operating data and low-level hardware control.
Whilst the BIOS is still the most widely used system, it’s quickly being taken over by it’s successor, Unified Extensible Firmware Interface.
CDN
CDN stands for Content Delivery Network and is responsible for delivering global information for huge systems 24 hours a day.
CDNs are great for providing faster load times, improved performance and load balancing. Instead of hosting all your images and videos on a single server, you can instead distribute your media on tons of servers around the world to distribute the load and reduce latency.
A great example of this is Netflix or Disney+, they often install machines as close as possible to ISP (I’ll cover ISP later 😉) locations to make sure your next movie loads as fast as possible.
CPU
A CPU is the Central Processing Unit and is referred to as the brain of a computer. Whilst it’s main up of multiple logical ‘units’, that’s a bit too in-depth for this list.
It’s responsible for executing instructions stored in the computer’s memory. Modern CPUs can perform billions of actions every second.
CRM
CRM stands for a Customer Relationship Management system and the main goal is to make business processes easier and more standardised.
This software typically includes asset management, sales pipelines, support and ticketing along with analytics to keep the number nerds in your business happy. Joking aside, a CRM is pretty much required for any modern business and tracking processes becomes exponentially more difficult.
CSS
CSS or Cascading Style Sheets is what’s used to style a website. It allows web developers to style a website or webapp without altering the HTML.
Options for editing include fonts, colours, animations and layouts.
DDOS
A Distributed Denial Of Service attack involves an attacking using lots of infected systems to concurrently vomit data towards a specific target. The aim of this attack is to make sure the target is overwhelmed and cannot handle genuine requests.
The most common way of generating large sources of traffic is through a botnet. This is where a criminal will attain a large number of devices that have common vulnerabilities. These devices could include printers, mobile phones, CCTV systems and may other poorly secured network devices.
DHCP
Dynamic Host Configuration Protocol is used on just about every single network on the planet. It’s makes it easy for devices to get an IP address. Rather than manually configuration a valid IP address and all the details that are needed, this protocol performs it automatically.
This is also useful for large enterprises as it allows for centralised management. Saves the IT guy running from machine to machine manually assigning IP information.
DNS
Domain Name System is something you use every single day without even realising it. Everything on the internet uses an IP address instead of a human readable name.
But instead of having to remember something like “132.33.2.4” to visit Facebook, you can instead just search for Facebook.com. DNS allows for these numerical addresses to be associated to an easier to remember name.
DOS
Denial of Service is similar to the previously mentioned DDOS attack, but the distinct difference is that a simple DOS attack relies on a single point of overwhelming traffic.
This attack isn’t used very often as it’s easy for providers like CloudFlare to just block the attacker.
HDD/SSD
You might have seen this if you’ve recently bought a new computer or laptop – And you’ll more commonly only see SSD in new devices. These stand for Hard Drive Disk and Solid State Drive.
They represent two different technologies for storing permanent data. With HDD using a spinning disk or platter, and SSDs using data chips. As I said earlier, modern devices will use SSDs as they are faster and have quickly caught up with HDD in terms of storage capacity and cost.
HTML
HTML or Hypertext Markup Language is the backbone of any website. It provides a set of elements and tags used to build layouts and structure.
Common elements include images, text, links and forms. HTML is very simple but deceptively powerful. HTML is also the formatting used in most modern email as it’s supported pretty much everywhere.
HTTP
Hypertext Transfer Protocol operates on the application-layer of the OSI model and is used for the transmittance and receiving of data over computer networks.
HTTP is responsible for structuring how web servers and web users facilitate a connection. It’s worth noting that this protocol is unsecured and information is used in plain text.
HTTPS
Building from HTTP, Hypertext Transfer Protocol Secure offers an encrypted connection between web servers and web users. This ensures that any sensitive information, such as addresses, bank details or passwords are protected from anyone else that might be intercepting the network traffic.
HTTPS is secured using SSL and TLS, both of which will be covered in this post!
ICMP
You likely haven’t heard of ICMP unless you are an IT or networking specialist. Internet Control Message Protocol provides methods for sending error messages and other information between computer network devices.
This is mainly used as a way to get error messages and information back from many devices, to a single centralised management solution. For example: if you have a bank of 20 switches, checking each one of them manually would be awful. So instead you can use ICMP to send all the info to a single dashboard for ease of management.
IMAP
Similar to the POP protocol, IMAP or Internet Message Access Protocol facilities email.
The main difference from POP however, is that IMAP offers more control and better features. It enabled multiple device support, organisation, and server side email. Allowing you to check, send and organise your emails on multiple devices around the world.
IoT
I’ve never seen a buzzword die as fast as this one did, Internet of Things was all the craze back in 2017 but hasn’t really progressed.
It refers to a network of physical machines, often small and simple, with embedded features that allows the devices to communicate between themselves.
IoT is a hugely broad term, ranging from your smartwatch to industrial equipment.
ISP
An Internet Service Provider is any company that provides an internet connection.
This might be to individuals or commercial buildings, but it’s the same thing. They typically offer a range of services in terms of pricing, speed and reliability.
The most common connection types are DSL, cable and fibre.
LAN
A Local Area Network is any computer network that operates over a very short geographical area. You have a LAN network in your home, although you usually just call it ‘the WiFi’. I’ve covered WiFi here!
These networks typically include phones, computers, printers etc. And they usually operate on three classes of IP addresses:
- Class A: 10.0.0.0 to 10.255.255.255
- Class B: 172.16.0.0 to 172.31.255.255
- Class C: 192.168.0.0 to 192.168.255.255
If you’ve had to fix your home internet, you might recognise an address in the 192.168.0.0 or 192.168.1.0 range as these are the most commonly used.
Thanks for reading 50 IT Acronyms And What They Mean!
You might like the following posts…
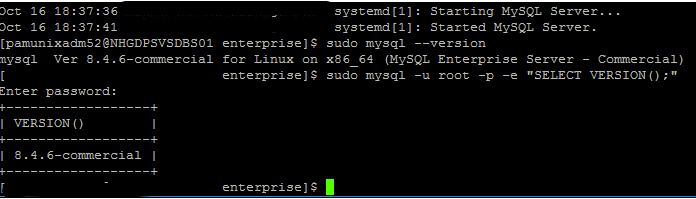
How to Optimise MySQL 8.4 on Windows
5 months since my last post! That’s what having a full-time job and a third…
How to Upgrade MySQL Community to MySQL Enterprise on Red Hat 9
Been a while since I made a post, so let’s jump straight back in with…
How to Setup WordPress Backups (FREE!)
Personally, I like my website. A lot. And I wouldn’t want one mistake to make…
Install NGINX on an Offline RHEL System – 2 Systems Required!
Been a while since my previous post, but let’s hope the magic hasn’t rubbed off…
MySQL 8.4 Replication with SSL on Ubuntu 22.02
So I recently wrote a post and made a YouTube video on setting up MySQL…
Gutenberg Just Broke my Website
More of a story and vent than an informative article. So to save you reading…
MAC
The Media Access Control or MAC Address is a unique identifier assigned to individual network adapters. Network adapters include Ethernet cards and WiFi cards.
It’s typically a permanently assigned identifier so that devices can be found on a computer network. There are ways to change your MAC address, but they typically require special software.
You might have heard of an IP address, but MAC addresses are more important but nowhere near as familiar. They are required for routers and switches to find where data packets need to be sent to and where they have come from.
NAS
NAS or Network Attached Storage is a simple way to have a ton of accessible storage over a computer network.
A NAS device is typically a small, single box used to house multiple hard drives. NAS devices built for home uses typically take 2 to 8 disks but enterprise hardware can quickly take 20+ disks and require a network rack.
Enterprise solutions typically offer redundant power, redundant network and specialised data protection schemas such as RAID, which is something I cover off here.
An example would be Synology, and this is the NAS I use at home.
NAT
Network Address Translation is the technique used in computer networks to translate IP addresses associated with a local private network, to a single public IP address accessible to the internet.
So you will have a WiFi connection at home, but your local IP isn’t the one used to visit websites on the internet. Instead, your router is assigned a public IP address by your ISP and NAT is responsible for translating traffic between these two locations.
This is important as it conserves public IP addresses and also aids security since your personal devices aren’t technically on the open internet.
OSI
The Open Systems Interconnect model is a framework used to standardise the communication between different devices on a computer network.
It does this by implementing several layers that each have their own specific function:
- 1) Physical
- 2) Data Link
- 3) Network
- 4) Transport
- 5) Session
- 6) Presentation
- 7) Application
I won’t cover each layer here – but know that each one is very important and have a distinct role to fill. This is a fundamental thing to understand when working with computer networks.
POP
Rather ridiculously named, the Post Office Protocol this is a very rudimental email service that actually deletes the emails from the server once they have been downloaded onto a client device.
Whilst it is still used today, it’s quiet rare as it takes away any possibilities of checking your emails on multiple devices or storing emails in organised folders on a server.
QoS
Quality of Service simply refers to how prioritised your computer network connection it. Network administrators and ISPs often utilise this function to make sure you receive the appropriate network bandwidth and latency.
Whilst it can be abused, it can often be very useful. Implementing QoS on a network primarily made up of printers and scanners, makes sense and there’s no reason a printer would need a 1Gb connection.
RAID
RAID has two acronyms that have changed slightly throughout the years. First standing for Redundant Array of Inexpensive Disks and now being more widely referred to as a Redundant Array of Independent Disks.
This technology allows multiple HDDs/SSDs to be logically grouped together. This helps increase overall capacity and redundancy. Whilst there are different types of RAID, the most common are RAID 1, RAID 0, RAID 10 and RAID5.
It’s worth noting, that RAID IS NOT A BACKUP. RAID shouldn’t be relied upon as a backup option as it’s simply a redundancy and capacity technique.
RAM
Random Access Memory is the short term memory used inside a computer to keep the most important information. This information is then ready at hand for use in the CPU, providing much faster access than other storage types.
This is volatile memory, meaning any information stored will be erased when the computer is shutdown.
The more RAM a system has, the more active programs and tasks it can work on simultaneously. The typical amount of RAM ranges from 16GB to 64GB for home machines.
RDP
This is a propriety technology created by Microsoft and is used to remotely access machines over a computer network. It stands for Remote Desktop Protocol and allows users to interact with remote desktops as if they were physically Infront of them.
Other features include sending and receiving files, running applications and allowing administrator access to programs.
It’s commonly used for IT support or connecting to remote servers in a datacentre somewhere.
SAN
A Storage Area Network is similar to a NAS however the distinct difference is that this is a networking dedicated to high-speed storage devices. It often connects these storage devices to other servers or to user machines.
They are really only seen in the enterprise space and allow a centralised management platform for a companies data. They must also be scalable, as they typically serve applications or databases that grow massively.
SATA
Serial Advanced Technology Attachment is the most widely used connector for modern computing hardware. You find it in just about every single laptop and desktop machine.
It replaced the Parallel ATA interface as it provider much faster transfer speeds. The cables used for SATA connections are also much smaller, allowing laptops to be more portable too.
SMB
Server Message Block is used in just about every single network share on the planet. It offers a simple yet powerful method of sharing documents from a single source.
It’s also cross-platform compatible, meaning that Windows, Linux and Mac devices can all access files and printers in the same way. Super useful for an enterprise setup.
SMTP
Another email protocol, Simple Mail Transfer Protocol allows emails to be sent and receiving over the internet. It’s the most common email protocol as it offers the most robust feature set.
Operating over port 25, by default it uses the client-server architecture which paves the way for more reliable and efficient email delivery.
SQL
This is the most common database language on the planet. Structured Query Language offers a standard set of rules when managing relational databases.
Typically, the operations are split into the CRUD acronym (Create, Read, Update, Delete) and the most common database offerings are MySQL, PostgreSQL and SQLite.
Microsoft also offers a propriety Windows MySQL Server offering that is used in enterprises.
SSL
Now succeeded by TLS, the Secure Socket Layer protocol enables secure communication over computer networks and the open internet.
Without this, any online website wouldn’t be able to securely encrypt it’s traffic. Leading to bank details and other sensitive information potentially being stolen by anyone listening to the traffic.
TCP/IP
The is a fundamental suite of networking protocols used for all communication over a computer network. Transmission Control Protocol/Internet Protocol offers a standard set of rules that allow data packets to be easily transmitted between different devices on the same network.
It consists of many layers, but in it’s most basic form it restricts manufacturers to abiding by a particular set of rules so that computer systems can talk to each other.
TLS
As mentioned in the SSL section, Transport Layer Security is now the de facto encryption protocol for securing internet traffic.
It provides everything modern systems need to stay secure, in a nice little package, including authentication, encryption and data integrity.
It’s used in most data communication networks, including: email; instant messaging and web browsing.
UI
Slightly less technical and more conceptual, is User Interface. It goes hand in hand with UX, and is vital when creating any digital product. Such as a website or app.
It relates to the graphical elements and controls that the user will need to use when using your product or website. Making sure your UI design is near enough perfect is very important. Having a product that is hard to use or understand, means less people want to use it.
Think of the last website or app you used that just looked perfect… That is good UI design.
URL
A Uniform Resource Locator is often referred to as a web address or website address. Consisting of many parts, such as the protocol, domain name and a specific path.
URLs provide a standardised method for publishing websites and webapps on the open internet.
Familiar URLs are: https://www.facebook.com, https://www.youtube.com and https://www.reddit.com.
URLs include the following sections:
- Protocol – This could be https, http, ftp etc. It determines how and what application is needed to access the URL
- Domain name – this could be facebook.com or reddit.com. Think of this as which house you want to visit on a street.
- Resource – This could be /home or /blog. Think of this as which room in the house you need to enter. Such as kitchen, living room etc.
USB
You’ll have heard of this before, definitely. It allows you to plug in almost any peripheral and use it. Most USB devices are plug-and-play, meaning no other drivers or software is required.
Standing for Universal Serial Bus, there are many version of this standard. Including: USB A, USB 2.0, USB C, USB 3.0; all of which have their pros and cons in terms of speed, reliability and capabilities.
UX
Building from UI, you have User Experience. This is a very nebulous term and can refer to any part of a product that the user interacts with.
The main goal of UX and UI is the build a system that makes the user feel like everything just kind of flows. Menus are exactly where they should be, tasks are simple and predictable and everything fits together in harmony.
The opposite to good UX design is a website with a bright red background, bright blue text and a broken menu that only works on desktop when you have your fingers crossed.
VNC
A Virtual Network Computing protocol is a way of remotely connecting to a machine as if you were right in front of it. Similar to RDP, although there are a bunch of different offerings that typically are opensource.
Most commonly, it’s used for remote IT support or connecting to servers across the globe that don’t run on Microsoft Windows.
VOIP
Voice over Internet Protocol does exactly what it says on the tin. It allows phone calls to be made over a traditional computer network rather than a dedicated phone line.
It converts the analogue signal from microphones, converts it to digital signals and transmits it over the network to the receiving end.
Other capabilities include video calls, conferencing and voicemail.
VPN
By now you will have heard of this term and might have even used it for yourself. A Virtual Private Network allows users to connect to different endpoints on the internet.
This can build security as they will appear to be browsing elsewhere and can also bypass local restrictions. For example, VPNs are often used to watch Netflix in other countries that have better libraries.
A more stand-up usage of VPNs, is to get around countrywide censorship, such as China and Russia.
VR
If you can remember AR from the beginning of this post, Virtual Reality is different as it completely builds a virtual world rather than enhancing or interacting with the real world.
This is typically achieved by wearing a VR headset and is used for games, work and other professional purposes. An example of this is Apple’s Vision Pro headsets.
Most headsets also have speakers to increase the immersion of the user. But many people still suffer from motion sickness after prolonged usage.
WiFi
Last but not least is WiFi. I bet you don’t know what it stands for do you?
Wireless Fidelity enables computer devices that are in close physical proximity to communicate without wires. Which is why this technology is normally seen in the home over your LAN connection.
Whilst there are different versions of WiFi, the most common are WiFi 5, 6 and 7. Which each generation offering higher throughput and more devices.
Conclusion
Well there you have it, 50 IT acronyms and they’re meanings.
I think my hands are going to fall off after all that typing!
If you want to reach out regarding my services, please use the link below:
Enjoy! 🎉